Breaking News
 Ukraine is not building one drone interceptor. It's building an air-deffence ecosystem.
Ukraine is not building one drone interceptor. It's building an air-deffence ecosystem.
 Resist The Surveillance State: 100 Ways to Fight Digital ID!
Resist The Surveillance State: 100 Ways to Fight Digital ID!
 Elon Musk: True - to 'not only have conservatives become vanishingly rare in academia...'
Elon Musk: True - to 'not only have conservatives become vanishingly rare in academia...'
 Trump Undecided on Moving Forward $14 Billion Arms Package for Taiwan After Talks With Xi
Trump Undecided on Moving Forward $14 Billion Arms Package for Taiwan After Talks With Xi
Top Tech News
 Sodium Ion Batteries Can Reach 100 Gigawatt Per Hour Per Year Scale in 2027
Sodium Ion Batteries Can Reach 100 Gigawatt Per Hour Per Year Scale in 2027
 Juiced Bikes proves capable electric motorcycles don't have to cost a lot
Juiced Bikes proves capable electric motorcycles don't have to cost a lot
 Headlight projectors turn your car into a drive-in theater
Headlight projectors turn your car into a drive-in theater
 US To Develop Small Modular Nuclear Reactors For Commercial Shipping
US To Develop Small Modular Nuclear Reactors For Commercial Shipping
 New York Mandates Kill Switch and Surveillance Software in Your 3D Printer ...
New York Mandates Kill Switch and Surveillance Software in Your 3D Printer ...
 Cameco Sees As Many As 20 AP1000 Nuclear Reactors On The Horizon
Cameco Sees As Many As 20 AP1000 Nuclear Reactors On The Horizon
 His grandparents had heart disease.
At 11, Laurent Simons decided he wanted to fight aging.
His grandparents had heart disease.
At 11, Laurent Simons decided he wanted to fight aging.
 Mayo Clinic's AI Can Detect Pancreatic Cancer up to 3 Years Before Diagnosis–When Treatment...
Mayo Clinic's AI Can Detect Pancreatic Cancer up to 3 Years Before Diagnosis–When Treatment...
A multi-terrain robot from China is going viral, not because of raw speed or power...
Quantum cryptography breakthrough may lead to more secure communications
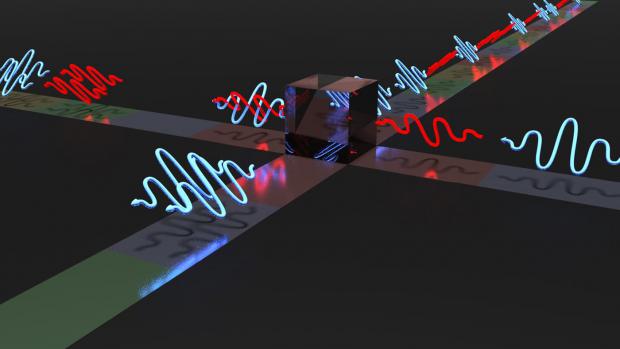
Many of the encryption methods that keep our online data safe rely on a digital key which is very hard for computers to crack – for instance, requiring the identification of two very large prime numbers, which standard computers are very poor at. But if a powerful quantum computer were to be built, it could crack these types of code with ease and jeopardize the safety of our digital communications.
The only encryption method that has been proven to be completely secure if applied correctly – quantum computers or not – is the so-called "one-time pad." Here's how it works: first, a secret digital key is created consisting of a completely random sequence of bits. The key is then securely sent to the receiver, and kept private. Now, the sender can encrypt his message by adding the message's bits to the random bits of the key. Under these conditions, the code is deemed truly uncrackable.
Keeping the key secret can be a challenge, but quantum physics can come to the rescue. That's because the weird and wonderful properties of quantum mechanics make it so that if someone were to try and intercept it, the key itself would change and both the sender and the receiver would immediately notice.

 The World's Biggest Fusion Reactor Just Hit A Milestone
The World's Biggest Fusion Reactor Just Hit A Milestone