Breaking News
 BREAKING: Federal Agents Descend on Suspected Somali Fraud Sites in Minneapolis (VIDEO)
BREAKING: Federal Agents Descend on Suspected Somali Fraud Sites in Minneapolis (VIDEO)
 BREAKING: Federal Agents Descend on Suspected Somali Fraud Sites in Minneapolis (VIDEO)
BREAKING: Federal Agents Descend on Suspected Somali Fraud Sites in Minneapolis (VIDEO)
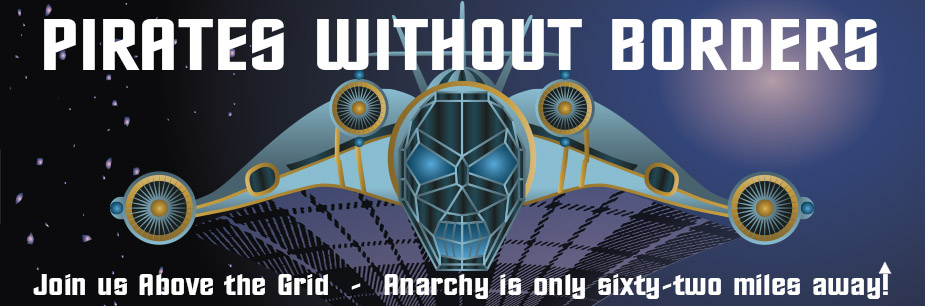
 Aargh! Letters of marque would unleash Blackbeard on the cartels
Aargh! Letters of marque would unleash Blackbeard on the cartels
 How a Barter System Could Sustain Communities During a Supply Chain Collapse
How a Barter System Could Sustain Communities During a Supply Chain Collapse
Top Tech News
 EngineAI T800: Born to Disrupt! #EngineAI #robotics #newtechnology #newproduct
EngineAI T800: Born to Disrupt! #EngineAI #robotics #newtechnology #newproduct
 This Silicon Anode Breakthrough Could Mark A Turning Point For EV Batteries [Update]
This Silicon Anode Breakthrough Could Mark A Turning Point For EV Batteries [Update]
 Travel gadget promises to dry and iron your clothes – totally hands-free
Travel gadget promises to dry and iron your clothes – totally hands-free
 Perfect Aircrete, Kitchen Ingredients.
Perfect Aircrete, Kitchen Ingredients.
 Futuristic pixel-raising display lets you feel what's onscreen
Futuristic pixel-raising display lets you feel what's onscreen
 Cutting-Edge Facility Generates Pure Water and Hydrogen Fuel from Seawater for Mere Pennies
Cutting-Edge Facility Generates Pure Water and Hydrogen Fuel from Seawater for Mere Pennies
 This tiny dev board is packed with features for ambitious makers
This tiny dev board is packed with features for ambitious makers
 Scientists Discover Gel to Regrow Tooth Enamel
Scientists Discover Gel to Regrow Tooth Enamel
 Vitamin C and Dandelion Root Killing Cancer Cells -- as Former CDC Director Calls for COVID-19...
Vitamin C and Dandelion Root Killing Cancer Cells -- as Former CDC Director Calls for COVID-19...
 Galactic Brain: US firm plans space-based data centers, power grid to challenge China
Galactic Brain: US firm plans space-based data centers, power grid to challenge China
Crypto user loses $50 million in 'address poisoning' scam

What to know:
A crypto user lost $50 million in USDT after falling for an "address poisoning" scam, where a scammer created a wallet address that closely resembled the intended destination address.
The scammer sent a small "dust" amount to the victim's transaction history, causing the victim to copy the address and send $49,999,950 USDT to the scammer's address.
The victim has published an onchain message demanding the return of 98% of the stolen funds within 48 hours, offering a $1 million white-hat bounty, and threatening legal escalation and criminal charges if the funds are not returned.
A crypto user lost $50 million in USDT after falling for an address poisoning scam in a massive onchain exploit.
The theft, spotted by Web3 security firm Web3 Antivirus, occurred after the user sent a $50 test transaction to confirm the destination address before transferring the rest of the funds.
Within minutes, a scammer created a wallet address that closely resembled the destination, matching the first and last characters, knowing most wallets abbreviate addresses and show only prefixes and suffixes.
The scammer then sent the victim a tiny "dust" amount to poison their transaction history. Seemingly believing the destination address was legitimate and properly entered, the victim copied the address from their transaction history and ended up sending $49,999,950 USDT to the scammer's address.
These small dust transactions are often sent to addresses with large holdings, poisoning transaction histories in an attempt to catch users in copy-paste errors, such as this one. Bots conducting these transactions cast a wide net, hoping for success, which they achieved in this case.
Blockchain data shows the stolen funds were then swapped for ether and moved across multiple wallets. Several addresses involved have since interacted with Tornado Cash, a sanctioned crypto mixer, in a bid to obfuscate the transaction trail.
In response, the victim published an onchain message demanding the return of 98% of the stolen funds within 48 hours. The message, backed with legal threats, offered the attacker $1 million as a white-hat bounty if the assets are returned in full.